Abstract
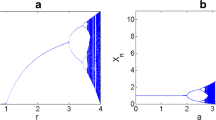
In this paper, a new image encryption scheme is proposed with high sensitivity to the plain image. In proposed scheme, two chaotic functions and logical operator xor are used. Image encryption process includes substitution of pixels and permutation. Using the new method of substitution, algorithm sensitivity somewhat has elevated to changes in the plain image that by changing a single pixel of the plain image, amount of NPCR reaches 100 %. Results of tests show that the cipher image does not give any information of statistical such as entropy, histogram and correlation of adjacent pixels to attackers. Also the proposed scheme has the wide key space and is so safe to the noise ratio and compression.










Similar content being viewed by others
Notes
Data Encryption Standard
International Data Encryption Algorithm
Rivest Shamir Adelman
Number of Pixels Change Rate
Unified Average Changing Intensity
References
Abd E-L, Ahmed A, Xiamu N (2013) A hybrid chaotic system and cyclic elliptic curve for image encryption. AEU-Int JElectron Commun 67(2):136–143
Abdullah, Abdul H, Rasul E, Malrey L (2012) A hybrid genetic algorithm and chaotic function model for image encryption. AEU-Int JElectron Commun 66(10):806–816
Bakhshandeh A, Eslami Z (2013) An authenticated image encryption scheme based on chaotic maps and memory cellular automata. Opt Lasers Eng 51(9):665–673
Behnia S, Akhshani A, Ahadpour S, Mahmodi H, Akhavan A (2007) A fast chaotic encryption scheme based on piecewise nonlinear chaotic maps. Phys Lett A 366(4):391–396
Bigdeli N, Farid Y, Afshar K (2012) A novel image encryption/decryption scheme based on chaotic neural networks. Eng Appl Artif Intell 25(4):753–765
François M, Grosges T, Barchiesi D, Erra R (2012) A new image encryption scheme based on a chaotic function. Signal Process Image Commun 27(3):249–259
Jiang J, Armstrong A, Guo-Can F (2004) Web-based image indexing and retrieval in JPEG compressed domain. Multimedia Systems 9(5):424–432
Norouzi, Benyamin, Seyed Mohammad S, Sattar M, Mohammad Reza M (2014) A novel image encryption based on hash function with only two-round diffusion process. Multimedia Systems 20(1):45–64
Pareek NK, Patidar V, Sud KK (2013) Diffusion-substitution based gray image encryption scheme. DigitSig Process 23(8):894–901
Patidar, Vinod NK, Pareek, Sud KK (2009) A new substitution–diffusion based image cipher using chaotic standard and logistic maps. Commun Nonlinear Sci Numer Simul 14(7):3056–3075
Song C-Y, Qiao Y-L, Zhang X-Z (2013) An image encryption scheme based on new spatiotemporal chaos. Opt-Int J Light Electron Opt 124(18):3329–3334
Tong X, Cui M (2008) Image encryption with compound chaotic sequence cipher shifting dynamically. Image Vis Comput 26(6):843–850
Wang Y, Wong K-W, Liao X, Chen G (2011) A new chaos-based fast image encryption algorithm. Appl Soft Comput 11(1):514–522
Wei X, Guo L, Zhang Q, Zhang J, Lian S (2012) A novel color image encryption algorithm based on DNA sequence operation and hyper-chaotic system. J Syst Softw 85(2):290–299
Yang H, Wong K-W, Liao X, Zhang W, Wei P (2010) A fast image encryption and authentication scheme based on chaotic maps. Commun Nonlinear Sci Numer Simul 15(11):3507–3517
Zhou Y, Karen P, Sos A, Chen CL (2012) Image encryption using P-Fibonacci transform and decomposition. Opt Commun 285(5):594–608
Zhu C (2012) A novel image encryption scheme based on improved hyperchaotic sequences. Opt Commun 285(1):29–37
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Parvin, Z., Seyedarabi, H. & Shamsi, M. A new secure and sensitive image encryption scheme based on new substitution with chaotic function. Multimed Tools Appl 75, 10631–10648 (2016). https://doi.org/10.1007/s11042-014-2115-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-014-2115-y