Abstract
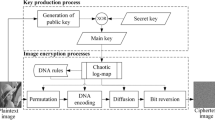
The meanings of passing information from one side to other side by a conventional way is been changed because of internet and communication technology. The issues of the security and the uprightness of information increase due to fast developments in digital world. Presently digital communication has become an important part of transmission of information securely. There are various internet applications which are utilized to convey covertly. As an outcome, the security of data against unapproved access has turned into a prime target. This leads to parts of advancement of different systems for information hiding. Cryptography and watermarking are famous techniques for hiding information accessible to conceal information safely. Our main goal here is to develop an innovative algebraic structures for the construction of nonlinear components of block cipher namely substitution boxes (S-boxes); and also use these components in image encryption and watermarking applications. Different types of S-boxes were introduced in literature based on Galois field and chaos theory in order to add confusion in any cryptosystems. The present construction is entirely based on Galois ring which enrich the existing algebraic structures of S-box theory.






Similar content being viewed by others
References
Abu Dahrouj FM (2008) Negacyclic and constacyclic codes over finite chain rings. Master of Mathematics Thesis, The Islamic University of Gaza
Abualrub T, Saip I (2007) Cyclic coacquired a great consideration in algebraic coding theory over the rings F 2 + uF 2 and F 2 + uF 2 + u 2 F 2. Des Codes Crypt 42:273–287
Adams C, Tavares S (1990) The structured design of cryptographically good S-boxes. J Crypt 3:27–41
Al-Ashker M (2005) Simplex codes over the ring ∑ s n = 0 u n F 2. Turk J Math 29(3):221–233
Al-Ashker M (2005) Simplex codes over F 2 + uF 2. Arab J Sci Eng 3:227–285
Al-Ashker M, Chen J (2013) Cyclic codes of arbitrary length over F q + uF q + ⋯ + u k − 1 F q . Palist J Math 2(1):72–80
Al-Ashker M, Hamoudeh M (2011) Cyclic codes over F 2 + uF 2 + ⋯ + u k − 1 F 2. Turk J Math 33:737–749
Andrade AA, Palazzo R (1999) Construction and decoding of BCH codes over finite rings. Linear Algebra Appl 286:69–85
Anees A, Ahmed Z (2015) A technique for designing substitution box based on van der pol oscillator. doi:10.1007/s11277-015-2295-4, Wireless Pers. Commun
Bilgin B, Nikova S, Nikov V, Rijmen V, Stutz G (2012) Thershold Implementations of all 3 × 3 and 4 × 4 S-boxes. Cryptographic Hardware and Embedded Systems. Springer Berlin Heidelberg 76–91
Bonnecaze A, Udaya P (1999) Cyclic codes and self dual codes over F 2 + uF 2. IEEE Trans Inf Theory 45:1250–1255
Cohen S, Niederreiter H (2009) Finite fields and applications. Cambridge University Press, London
Cui L, Cao Y (2007) A new S-box structure named Affine-Power-Affine. Int J Innov Comput Appl 3(3):45–53
Daemen J, Rijmen V. The block cipher Rijndael. NIST’s AES
Khan M, Shah T (2014) A novel image encryption technique based on Hénon chaotic map and S8 symmetric group. Neural Comput Appl 25:1717–1722
Li X, Li B, Yang B, Zeng T (2013) General framework to histogram shifting based reversible data hiding. IEEE Trans Image Process 22:2181–2191
Liu Z, Zhang F, Wang J, Wang H, Huang J (2016) Authentication and recovery algorithm for speech signal based on digital watermarking. Signal Process 123:157–166
Naji A (2002) Linear codes over F 2 + uF 2 + u 2 F 2 of Constant Lee weight. The second conference of the Islamic University on Mathematical Science-Gaza
Qian J, Li Z, Zhu S (2006) Constacyclic and cyclic codes over F 2 + uF 2 + u 2 F 2. IEICE Trans Fundam 6:1863–1885
Qian J, Zhang L, Zhu S (2005) Cyclic codes over F p + uF p + ⋯ + u k − 1 F p . IEICE Trans Fundam 3:795–779
Qian J, Zhang L, Zhu S (2006) (1+u) constacyclic and cyclic over F 2 + uF 2. Appl Math Lett 19(8):823–820
Qin C, Chang C-C, Chiu Y-P (2014) A novel joint data-hiding and compression scheme based on SMVQ and image inpainting. IEEE Trans Image Process 23:969–978
Qin C, Zhang X (2015) Effective reversible data hiding in encrypted image with privacy protection for image content. J Vis Commun Image Represent 31:154–164
Qin C, Chang C-C, Hsu T-J (2015) Reversible data hiding scheme based on exploiting modification direction with two steganographic images. Multimedia Tools Appl 74:5861–5872
Rijmen V. Efficient Implementation of the Rijndael S-box. Katholieke Universiteit Leuven, Dept. ESAT, Kard. Mercierlaan 94, B--3001 Heverlee, Belgium
Sajjad M, Ejaz N, Baik SW (2014) Multi-kernel based adaptive interpolation for image super-resolution. Multimed Tools Appl 72:2063–2085
Selvarajah S, Kodituwakku SR (2011) Analysis and comparison of texture features for content based image retrieval. Int J Latest Trends Comput 2:108–113
Shah T, Qamar A, Hussain I (2013) Substitution box on maximal cyclic subgroup of units of a Galois ring. Z Naturforsch A 68a:567–572
Shanbhag AG, Kumar PV, Helleseth T (1996) Upper bound for a hybrid sum over Galois rings with applications to aperiodic correlation of some q-ary sequences. IEEE Trans Inf Theory 42(1):250–54
Shankar P (1979) On BCH codes over arbitrary integer rings. IEEE Trans Inf Theory IT-25(4):480–483
Tran MT, Bui DK, Doung AD (2008) Gray S-box for advanced encryption standard. Int Conf Comput Intell Secur 1:253–256
Yi X, Cheng SX, You XH, Lam KY (2002) A method for obtaining cryptographically strong 8×8 S-boxes. Int Conf Inf Netw Appl 2(3):14–20
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Khan, M., Shah, T. & Batool, S.I. A new approach for image encryption and watermarking based on substitution box over the classes of chain rings. Multimed Tools Appl 76, 24027–24062 (2017). https://doi.org/10.1007/s11042-016-4090-y
Received:
Revised:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11042-016-4090-y